Manage Risk
From Every Angle
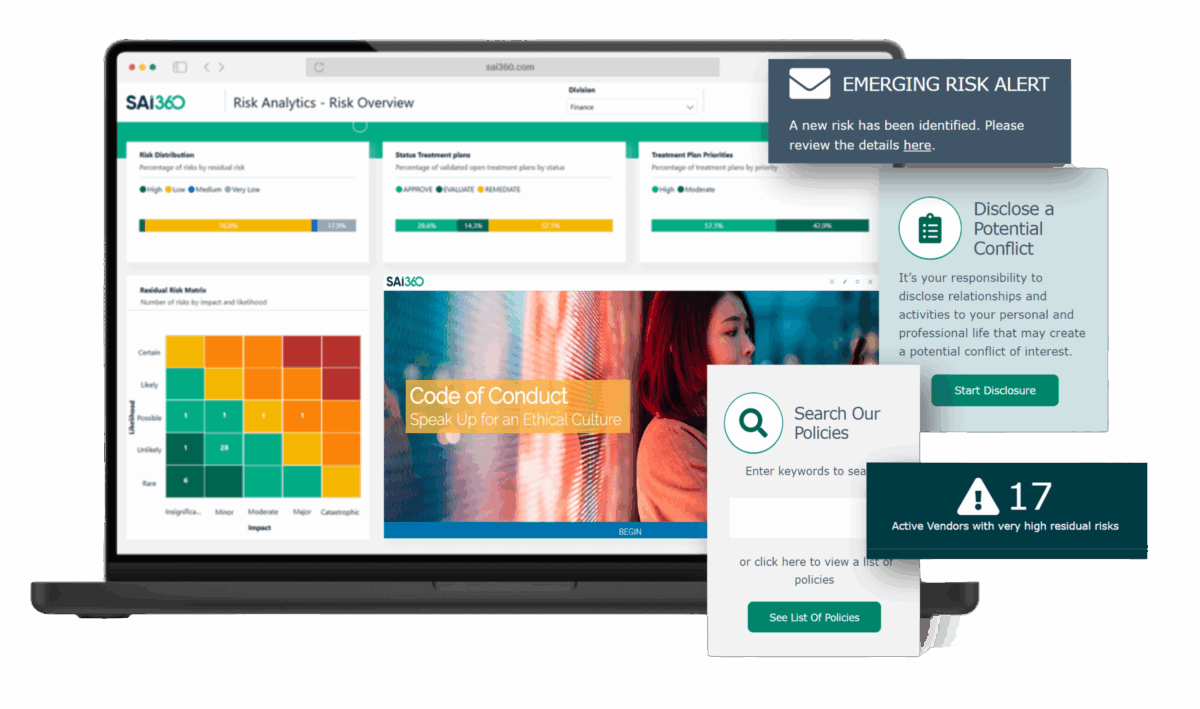
In a world of accelerating risk, organizations need more than check-the-box compliance – they need connected, intelligent GRC.
The SAI360 GRC Platform helps organizations seamlessly balance ethics, risk, and compliance with an integrated software solution that manages all types of risks while supporting a risk-aware compliance program.
One Platform.
Multiple Angles.
The SAI360 GRC Platform helps organizations seamlessly balance ethics, risk, and compliance with an integrated solution that manages all types of risks while supporting a risk-aware compliance program.
- Unify governance processes across multiple functions to break down silos
- Connect compliance management, risk management, policy administration and compliance training for a holistic approach
- Leverage risk insights and behavioral analytics – all to help you adapt to new risks and regulations while building your ethical culture