Integrated GRC from Every Angle
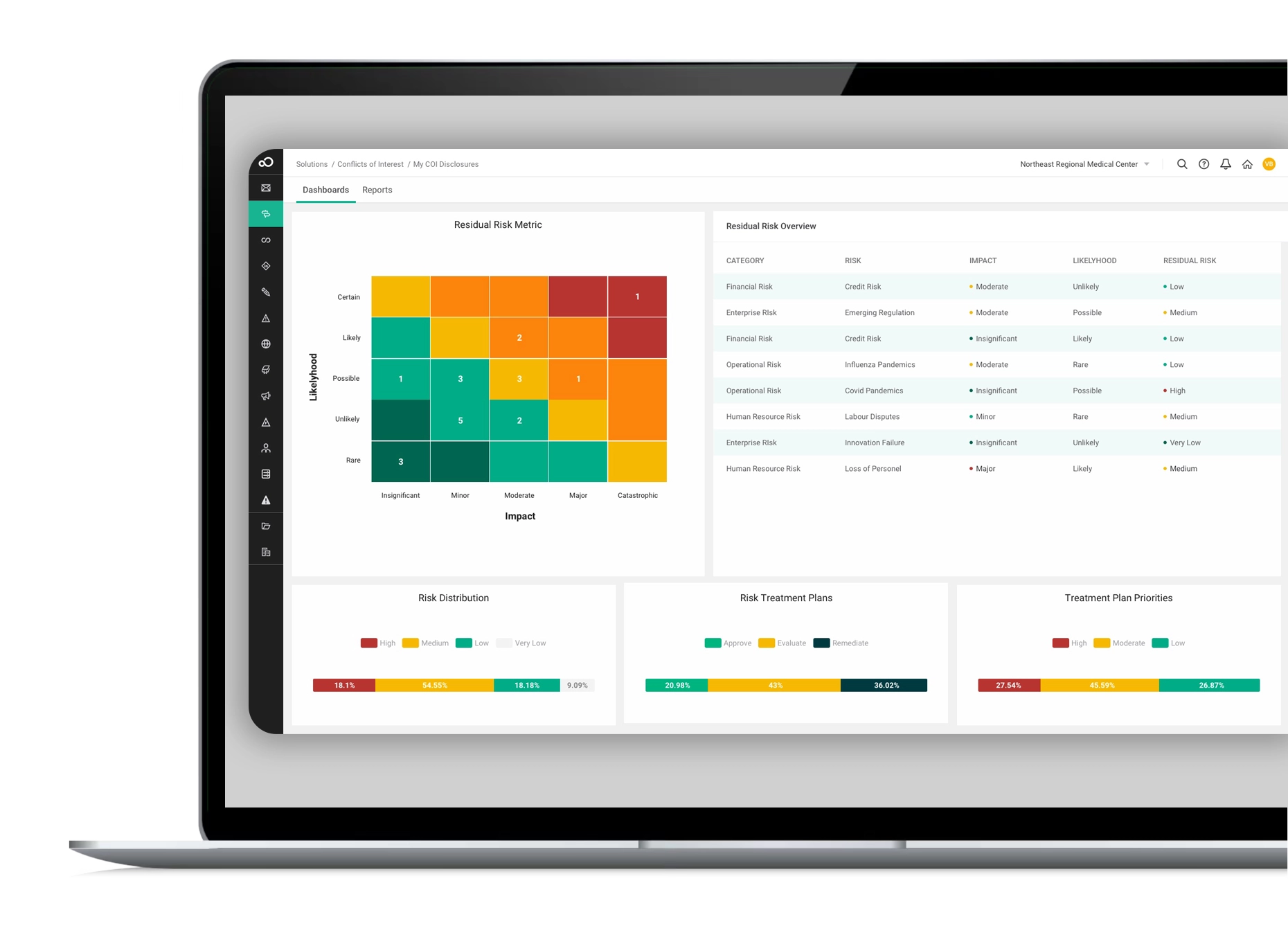
Gain a comprehensive view of risks to make informed decisions, effectively managing threats and seizing opportunities from every angle. With compliance training software and compliance elearning, employees are equipped to handle complex compliance and risk management software effectively, ensuring a robust and resilient organization. Our GRC software solutions pave the way to a secure, compliant, and prosperous future. Choose from 20+ preconfigured modules, including:
Integrated modules tailored to fit your needs
These GRC software modules enable you to oversee, control, and proactively address disruptions, safeguarding your business. With the capacity to span enterprise-wide, our governance and risk compliance software offers a unified solution for comprehensive risk management across all facets of your organization, ensuring a seamless fit for your requirements.

Industry-leading technology delivering efficiency and security
Our GRC software is powered by cutting-edge technology, featuring seamless workflow, robust integrations, advanced reporting, AI capabilities, top-tier security, and a cloud-based platform. Best practice modules and professional services further enhance its effectiveness, providing a comprehensive GRC solution for streamlined and secure risk management.

“When you find a great company like SAI360, you stick with them! I like the personal attention from the SAI360 staff, who ensure I can get my job done efficiently and produce a quality product.”
Worldwide Frameworks, Standards and Regulations
SAI360 offers built-in, pre-mapped standards and controls to support your specific compliance requirements, wherever you are in the world, making operationalizing governance risk and compliance software easier and faster. The integration of compliance training software ensures that employees are well-prepared to meet these standards, streamlining compliance and risk management across your organization.
FAQs
Interested in learning more about SAI360’s Governance, Risk, and Compliance (GRC) capabilities?
Fill out the form to start a conversation.








